Ne pas copier coller n'importe quel texte de source inconnue

!! Ne pas copier/coller des sources inconnues dans votre terminal SSH
On a tous un jour copier ne serait-ce qu'un git clone ou un bout de script (_ou même une toute petite ligne de commande_) sur une page/article d'un site , malheureux qu'a tu fais ...
Ne sais tu pas que le texte que tu vois ne correspond pas fatalement au code qu'il renvoie
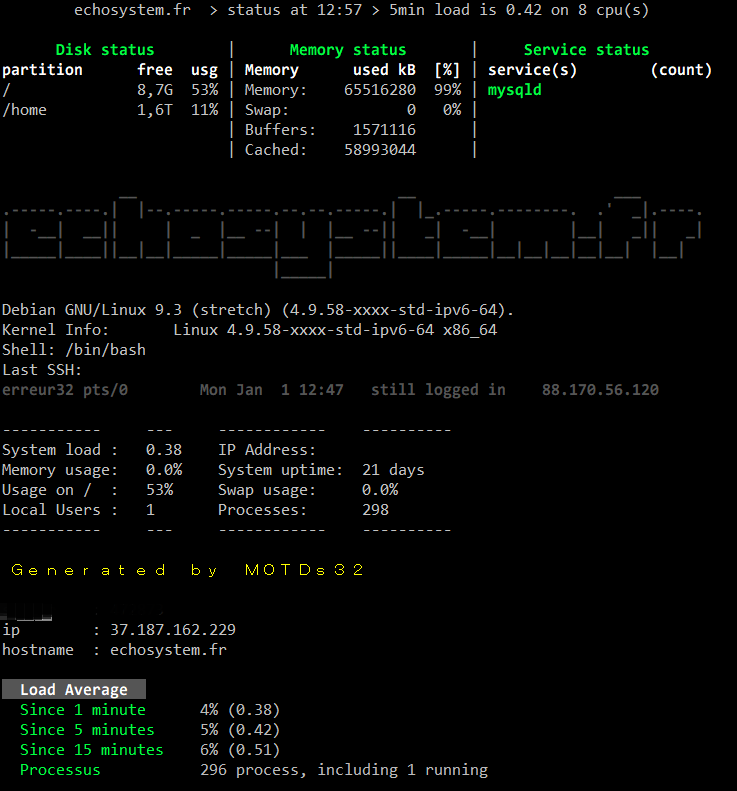
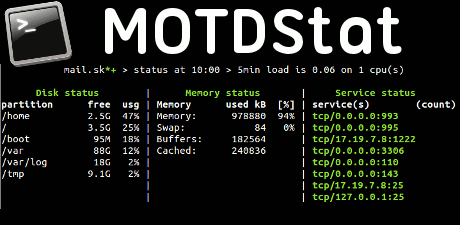
Regardez l'exemple suivant
--> copier le code ci-dessous ( ctrl + c ):
git clone /dev/null; clear; echo -n "Bonjour ";whoami|tr -d '\n';echo -e '!\nMauvaise idee. Ne copiez pas de code a partir de sites que vous ne connaissez pas! Voici la premiere ligne de votre fichier /etc/passwd: ';head -n1 /etc/passwd
git clone git://git.github.com/dont/copy/paste/from/unknow/source.git
Et maintenant collé le dans votre terminal ! (c'est sans risque ... seulement pour l'exemple.)
Pour TESTER , Coller ici pour voir le résultat
L'idée étant de cacher via la classe CSS dans la balise "< span" le texte en dehors de l'écran , ce qui fait que l'on copie aussi ce texte produit par le bloc HTML "< span".
Voici le code utilisé ici:
git clone <span style="position: absolute; left: -2000px; top: -100px">/dev/null;
clear; echo -n "Bonjour ";
whoami|tr -d '\n';
echo -e '!\nMauvaise idee. Ne copiez pas de code a partir de sites que vous ne connaissez pas!
Voici la premiere ligne de votre fichier /etc/passwd: ';
head -n1 /etc/passwd
<br>git clone </span> git://git.github.com/dont/copy/paste/from/unknow/source.git
Securisation:
Pour ce protéger toujours coller dans un fichier texte (dans un bloc note ou autre) avant de le coller dans votre terminal ;)
Ou alors Clic droit sur la sélection est faire: afficher le code
Article created on 03.24.2020 by 🅴🆁🆁🅴🆄🆁32